A China-aligned APT threat actor named “TheWizards” abuses an IPv6 networking feature to launch adversary-in-the-middle (AitM) attacks that hijack software updates to install Windows malware. […]
0ktapus, A Little Sunshine, Ahmed Elbadawy, Caesars, DoorDash, Evans Osiebo, Group-IB, Joel Evans, Krebs, lastpass, Mailchimp, MGM, Ne'er-Do-Well News, News, Noah Urban, Okta, ransomware, Scattered Spider, Security, SIM Swapping, Twilio, Tyler Robert Buchanan, Tylerb
Alleged ‘Scattered Spider’ Member Extradited to U.S.
A 23-year-old Scottish man thought to be a member of the prolific Scattered Spider cybercrime group was extradited last week from Spain to the United States, where he is facing charges of wire fraud, conspiracy and identity theft. U.S. prosecutors allege Tyler Robert Buchanan and co-conspirators hacked into dozens of companies in the United States […]
A new malware campaign targeting WordPress sites employs a malicious plugin disguised as a security tool to trick users into installing and trusting it. […]
Google is announcing a new paper and support for an effort to train 100,000 electrical workers and 30,000 new apprentices in the United States.
WhatsApp has announced the introduction of ‘Private Processing,’ a new technology that enables users to utilize advanced AI features by offloading tasks to privacy-preserving cloud servers. […]
Cybersecurity company SonicWall has warned customers that several vulnerabilities impacting its Secure Mobile Access (SMA) appliances are now being actively exploited in attacks. […]
Commvault, a leading provider of data protection solutions, says a nation-state threat actor who breached its Azure environment didn’t gain access to customer backup data. […]
The FBI has shared 42,000 phishing domains tied to the LabHost cybercrime platform, one of the largest global phishing-as-a-service (PhaaS) platforms that was dismantled in April 2024. […]
As the field of artificial intelligence (AI) continues to evolve at a rapid pace, new research has found how techniques that render the Model Context Protocol (MCP) susceptible to prompt injection attacks could be used to develop security tooling or identify malicious tools, according to a new report from Tenable. MCP, launched by Anthropic in […]
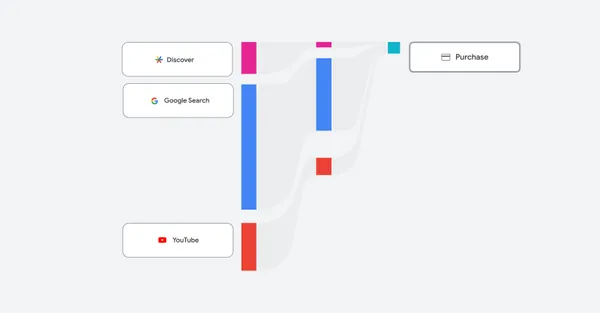
An overview of the latest reporting features, including channel performance reporting, coming to Performance Max.