Originally published by Diligent.The EU AI Act comes into force on 1 August 2024. It is the world’s first comprehensive legislation designed to address artificial intelligence (AI) risks by establishing a set of rules and obligations aimed at safeguarding the health, safety, and fundamental rights of EU citizens. In doing so, it seeks to support […]
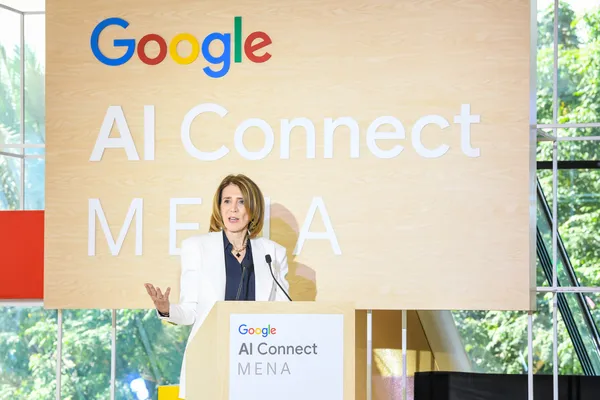
Google is committed to make benefits of AI more accessible and inclusive for everyone in the Middle East and North Africa.
Browse 2024’s most popular gift ideas with Google Shopping’s Holiday 100.
Behavioral analytics, long associated with threat detection (i.e. UEBA or UBA), is experiencing a renaissance. Once primarily used to identify suspicious activity, it’s now being reimagined as a powerful post-detection technology that enhances incident response processes. By leveraging behavioral insights during alert triage and investigation, SOCs can transform their workflows to become more
STALKER 2: Heart of Chornobyl is now available for pre-load on Xbox Series, requiring around 146 GB of storage. The post You can now pre-load STALKER 2 on Xbox Series X/S at a whopping 146 GB appeared first on MSPoweruser.
Ecosia and Qwant are creating a European search index called EUSP to reduce dependence on US tech like Google and Bing. The post No more Google reliance, says EU, so it’s building its own European search index appeared first on MSPoweruser.
Cybersecurity researchers have flagged a new ransomware family called Ymir that was deployed in an attack two days after systems were compromised by a stealer malware called RustyStealer. “Ymir ransomware introduces a unique combination of technical features and tactics that enhance its effectiveness,” Russian cybersecurity vendor Kaspersky said. “Threat actors leveraged an unconventional blend
Apple has added a new security feature with the iOS 18.1 update released last month to ensure that iPhones automatically reboot after long idle periods to re-encrypt data and make it harder to extract. […]
VMware has announced that its VMware Fusion and VMware Workstation desktop hypervisors are now free to everyone for commercial, educational, and personal use. […]
A new ransomware family called ‘Ymir’ has been spotted in the wild, being introduced onto systems that were previously compromised by the RustyStealer info-stealer malware. […]