New York State has announced a $2,000,000 settlement with PayPal over charges it failed to comply with the state’s cybersecurity regulations, leading to a 2022 data breach. […]
Zyxel is warning that a bad security signature update is causing critical errors for USG FLEX or ATP Series firewalls, including putting the device into a boot loop. […]
Learn about how Google tests products like Pixel phones to protect against the elements.
Microsoft has reminded Windows administrators that driver synchronization in Windows Server Update Services (WSUS) will be deprecated on April 18, 90 days from now. […]
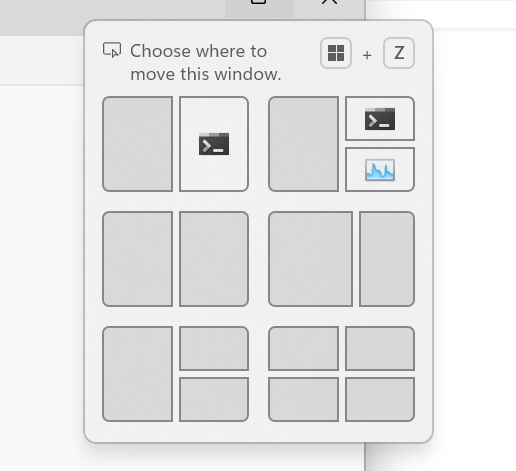
Hello Windows Insiders, today we are releasing Windows 11 Insider Preview Build 22635.4805 (KB5050105) to the Beta Channel. Changes in Beta Channel builds and updates are documented in two buckets: new features, improvements, and fixes that are being gradually rolled out for Insiders who have turned on the toggle to get the latest updates as […]
Hello Windows Insiders, today we are releasing Windows 11 Insider Preview Build 26120.3000 (KB5050103) to the Dev Channel. Changes in Dev Channel builds and updates are documented in two buckets: new features, improvements, and fixes that are being gradually rolled out for Insiders who have turned on the toggle to get the latest updates as […]
Security researchers have discovered an arbitrary account takeover flaw in Subaru’s Starlink service that could let attackers track, control, and hijack vehicles in the United States, Canada, and Japan using just a license plate. […]
A North Korean threat group has been using a technique called RID hijacking that tricks Windows into treating a low-privileged account as one with administrator permissions. […]
NotebookLM Plus can be used for businesses and larger organizations. Here are five tips to get started with NotebookLM.
A threat actor targeted low-skilled hackers, known as “script kiddies,” with a fake malware builder that secretly infected them with a backdoor to steal data and take over computers. […]