There are tons of new features to check out in the Gemini app, from personalization to real-time collaboration. In the latest episode of the Google AI: Release Notes pod…
The UK’s National Cyber Security Centre (NCSC) has published specific timelines on migrating to post-quantum cryptography (PQC), dictating that critical organizations should complete migration by 2035. […]
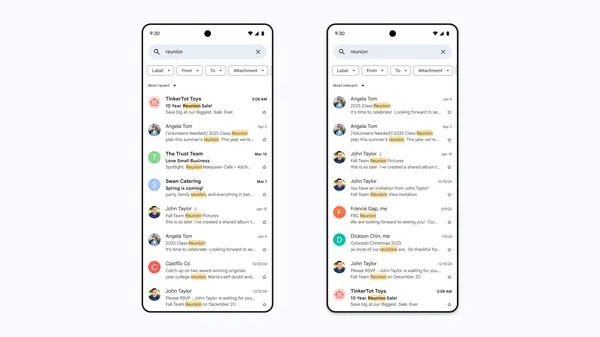
If you’ve ever struggled with finding information in your overflowing inbox, you’re not alone. That’s why Gmail is rolling out a smarter search feature powered by AI to …
YouTube videos promoting game cheats are being used to deliver a previously undocumented stealer malware called Arcane likely targeting Russian-speaking users. “What’s intriguing about this malware is how much it collects,” Kaspersky said in an analysis. “It grabs account information from VPN and gaming clients, and all kinds of network utilities like ngrok, Playit, Cyberduck, […]
Popular WordPress security plugin WP Ghost is vulnerable to a critical severity flaw that could allow unauthenticated attackers to remotely execute code and hijack servers. […]
The compromise of GitHub Action tj-actions/changed-files has impacted only a small percentage of the 23,000 projects using it, with it estimated that only 218 repositories exposed secrets due to the supply chain attack. […]
Microsoft has lifted an upgrade block that prevented Asphalt 8: Airborne players from upgrading their systems to Windows 11 24H2 due to compatibility issues. […]
Annual pentests can leave security gaps that attackers can exploit for months. Learn more from Outpost24 about why continuous penetration testing (PTaaS) offers real-time detection, remediation, and stronger protection. […]
Swiss global solutions provider Ascom has confirmed a cyberattack on its IT infrastructure as a hacker group known as Hellcat targets Jira servers worldwide using compromised credentials. […]
Veeam has released security updates to address a critical security flaw impacting its Backup & Replication software that could lead to remote code execution. The vulnerability, tracked as CVE-2025-23120, carries a CVSS score of 9.9 out of 10.0. It affects 12.3.0.310 and all earlier version 12 builds. “A vulnerability allowing remote code execution (RCE) by […]