The UK Information Commissioner’s Office (ICO) has fined Advanced Computer Software Group Ltd £3.07 million over a 2022 ransomware attack that exposed the sensitive personal data of 79,404 people, including National Health Service (NHS) patients. […]
Despite Oracle denying a breach of its Oracle Cloud federated SSO login servers and the theft of account data for 6 million people, BleepingComputer has confirmed with multiple companies that associated data samples shared by the threat actor are valid. […]
Cloud-based streaming company StreamElements confirms it suffered a data breach at a third-party service provider after a threat actor leaked samples of stolen data on a hacking forum. […]
A new cybercrime platform named ‘Atlantis AIO’ provides an automated credential stuffing service against 140 online platforms, including email services, e-commerce sites, banks, and VPNs. […]
Hello Windows Insiders, today we are releasing Windows 11 Insider Preview Build 27823 to the Canary Channel. We are also not planning to release SDKs for 27xxx series builds for the time being. Changes and Improvements [General] This update includes a small set of general improvements and fixes that improve the overall experience for Insiders […]
The Chinese threat actor known as FamousSparrow has been linked to a cyber attack targeting a trade group in the United States and a research institute in Mexico to deliver its flagship backdoor SparrowDoor and ShadowPad. The activity, observed in July 2024, marks the first time the hacking crew has deployed ShadowPad, a malware widely […]
Claude could be getting a ChatGPT-like Deep Research feature called Compass. You can tell Claude’s Compass what you need, and the AI agent will take care of everything. […]
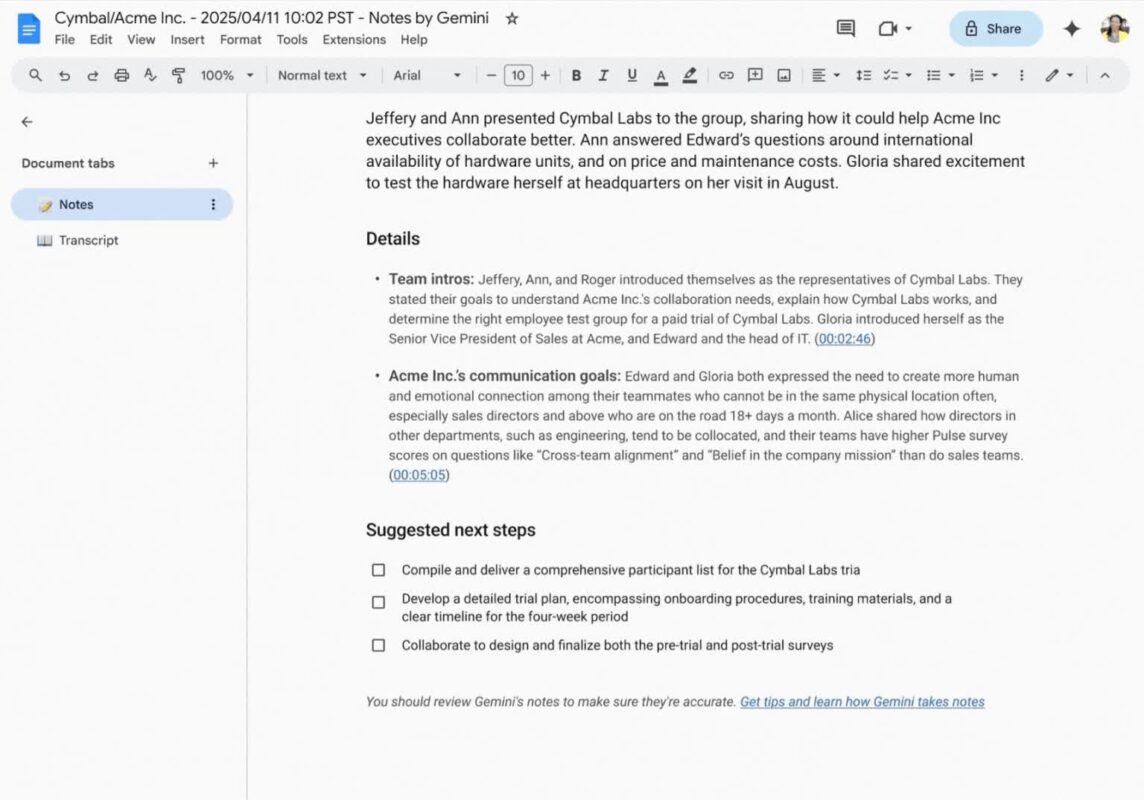
Our latest Workspace drop is here and includes some helpful Gemini updates for Google Meet business users. Here are few new things to try:The “Take notes for me” feature…
Brandcast, YouTube’s annual Upfront event, is happening on May 14 at Lincoln Center in New York. At the event, advertisers will learn how to harness the power of YouTube…
230M stolen passwords met complexity requirements—and were still compromised. Passwords aren’t going away for now, but there are new technologies that may increasingly replace them. Learn more from Specops Software about how to protect your passwords. […]