Nine VSCode extensions on Microsoft’s Visual Studio Code Marketplace pose as legitimate development tools while infecting users with the XMRig cryptominer to mine Ethereum and Monero. […]
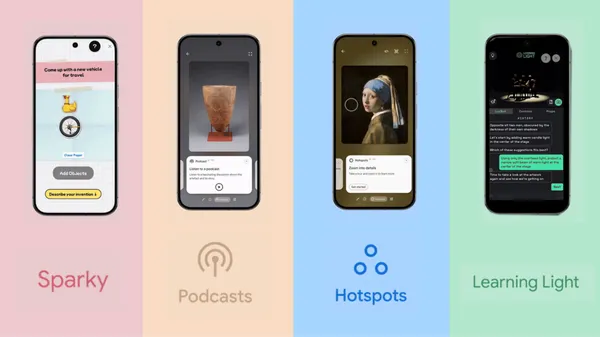
Google Arts & Culture has launched new AI experiments to help you explore hidden artwork details, stage lighting design and more.
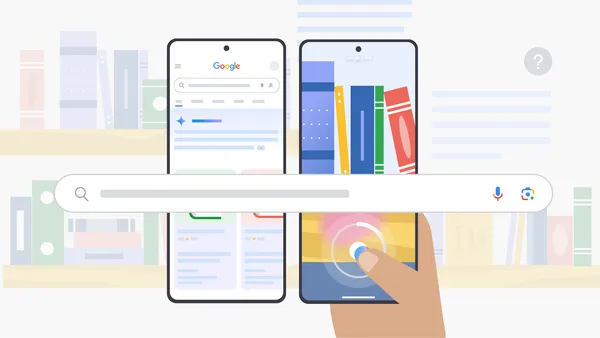
We’re bringing the powerful multimodal capabilities in Lens to AI Mode.
US food giant WK Kellogg Co is warning employees and vendors that company data was stolen during the 2024 Cleo data theft attacks. […]
Microsoft has introduced a new Windows 11 24H2 safeguard hold for systems running security or enterprise software using SenseShield Technology’s sprotect.sys driver. […]
Cybersecurity agencies from Australia, Canada, New Zealand, and the United States have published a joint advisory about the risks associated with a technique called fast flux that has been adopted by threat actors to obscure a command-and-control (C2) channel. “‘Fast flux’ is a technique used to obfuscate the locations of malicious servers through rapidly changing […]
Originally published by Valence. Written by Jason Siberman. The rise of SaaS applications has transformed the way organizations operate, enabling greater collaboration, agility, and efficiency. Business-critical tools such as Salesforce, HubSpot, Workday, NetSuite, and GitHub are essential for departments like sales, marketing, HR, finance, and R&D. These tools empower teams to work independently, adopt […]
Learn more about how Google Maps is using AI to fight fake business information.
You have until April 27 at 11:59 p.m. PT to grab lifetime access to AdGuard’s privacy and ad-blocking tools for just $15.97 (reg. $169)—remember to enter code FAMPLAN at checkout for this limited-time discount. […]
Gemini Live with video and screen sharing is now rolling out to Android mobile devices.