A hacking group dubbed ‘Elusive Comet’ targets cryptocurrency users in social engineering attacks that exploit Zoom’s remote control feature to trick users into granting them access to their machines. […]
Category Archives: News
Microsoft has released the optional KB5055612 preview cumulative update for Windows 10 22H2 with two changes, including a fix for a GPU paravirtualization bug in Windows Subsystem for Linux 2 (WSL2). […]
South Korea’s largest mobile operator, SK Telecom, is warning that a malware infection allowed threat actors to access sensitive USIM-related information for customers. […]
Google Fi Wireless launches a new, more affordable Unlimited Essentials plan, more high-speed data on existing plans, major iOS improvements and limited time promotions.
Cybersecurity researchers have detailed a malware campaign that’s targeting Docker environments with a previously undocumented technique to mine cryptocurrency. The activity cluster, per Darktrace and Cado Security, represents a shift from other cryptojacking campaigns that directly deploy miners like XMRig to illicitly profit off the compute resources. This involves deploying a malware strain
The recommended Ripple cryptocurrency NPM JavaScript library named “xrpl.js” was compromised to steal XRP wallet seeds and private keys and transfer them to an attacker-controlled server, allowing threat actors to steal all the funds stored in the wallets. […]
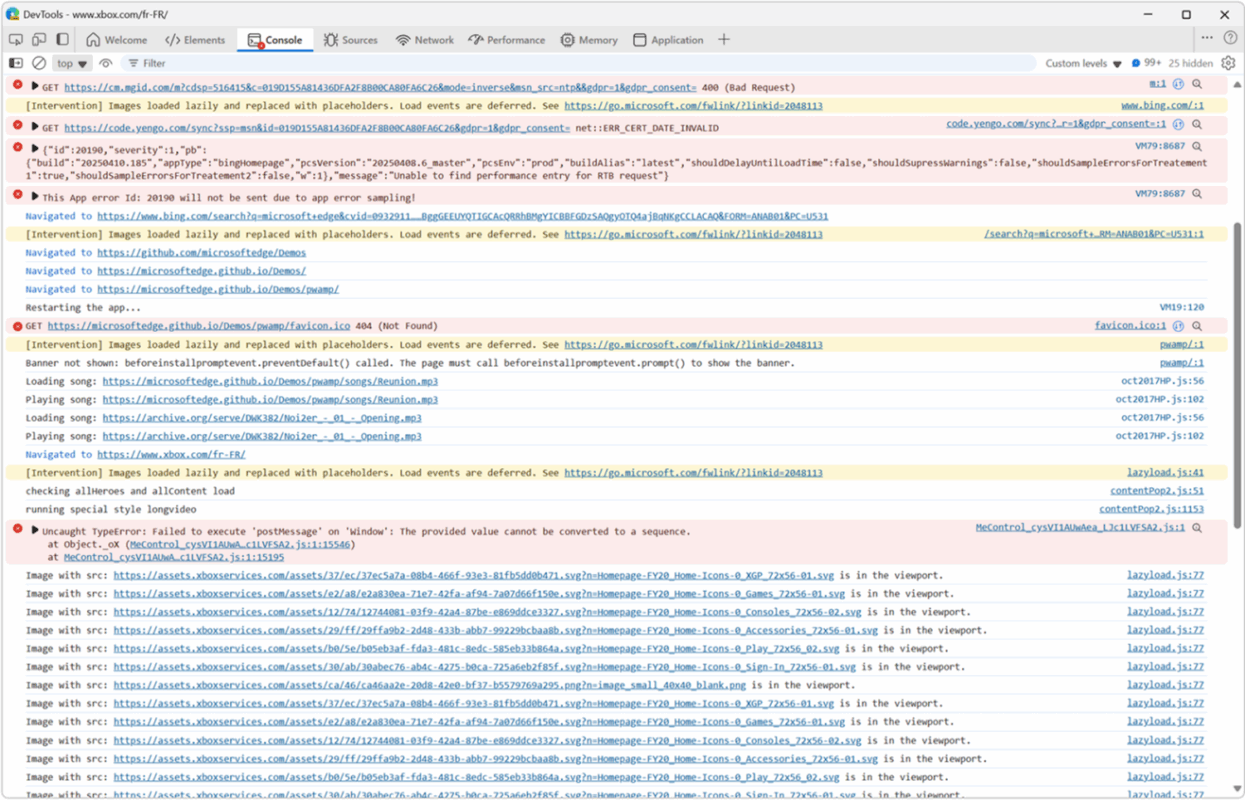
If you work on a large enough code base involving multiple teams at your organization, you probably have to deal with large amounts of logs when inspecting your webapp. This is an area that we’re interested in improving, and are proposing a new feature, based on the console.context() method, to enable helpful contextual logging in […]
The Cloud Controls Matrix (CCM) is a framework of essential cloud security controls that follow CSA best practices. You can use CCM to assess and guide the security of any cloud implementation. CCM also provides guidance on which actors within the cloud supply chain should implement which security controls. Both cloud service customers (CSCs) and […]
A proof-of-concept attack called “Cookie-Bite” uses a browser extension to steal browser session cookies from Azure Entra ID to bypass multi-factor authentication (MFA) protections and maintain access to cloud services like Microsoft 365, Outlook, and Teams. […]
Cybersecurity researchers have detailed a now-patched vulnerability in Google Cloud Platform (GCP) that could have enabled an attacker to elevate their privileges in the Cloud Composer workflow orchestration service that’s based on Apache Airflow. “This vulnerability lets attackers with edit permissions in Cloud Composer to escalate their access to the default Cloud Build service account, […]