Google’s newest power purchase agreement (PPA) with Shell is the first time a corporate PPA has extended the lifespan of an offshore wind farm1. This agreement will exte…
Category Archives: News
Google has released its monthly security updates for Android with fixes for 46 security flaws, including one vulnerability that it said has been exploited in the wild. The vulnerability in question is CVE-2025-27363 (CVSS score: 8.1), a high-severity flaw in the System component that could lead to local code execution without requiring any additional execution […]
A recently disclosed critical security flaw impacting the open-source Langflow platform has been added to the Known Exploited Vulnerabilities (KEV) catalog by the U.S. Cybersecurity and Infrastructure Security Agency (CISA), citing evidence of active exploitation. The vulnerability, tracked as CVE-2025-3248, carries a CVSS score of 9.8 out of a maximum of 10.0. “Langflow contains a […]
The data-theft extortion group known as Luna Moth, aka Silent Ransom Group, has ramped up callback phishing campaigns in attacks on legal and financial institutions in the United States. […]
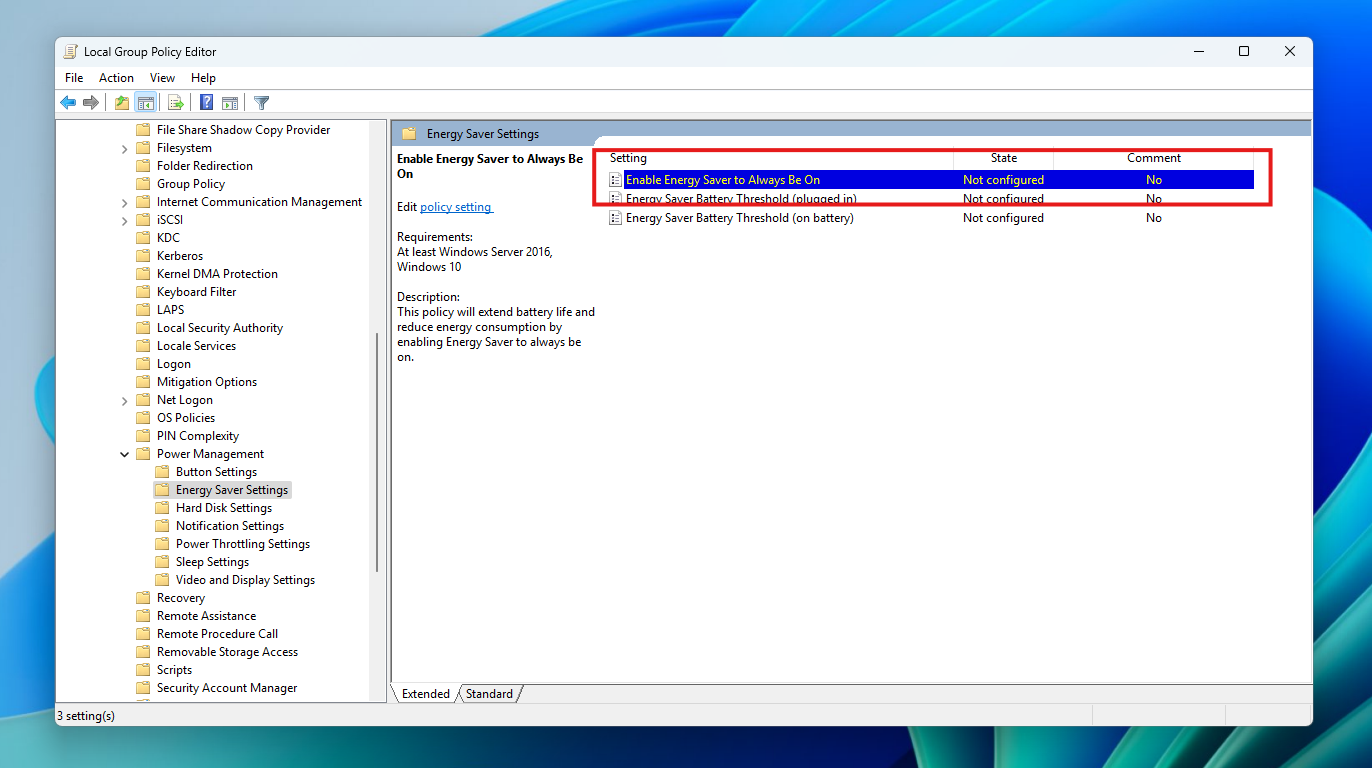
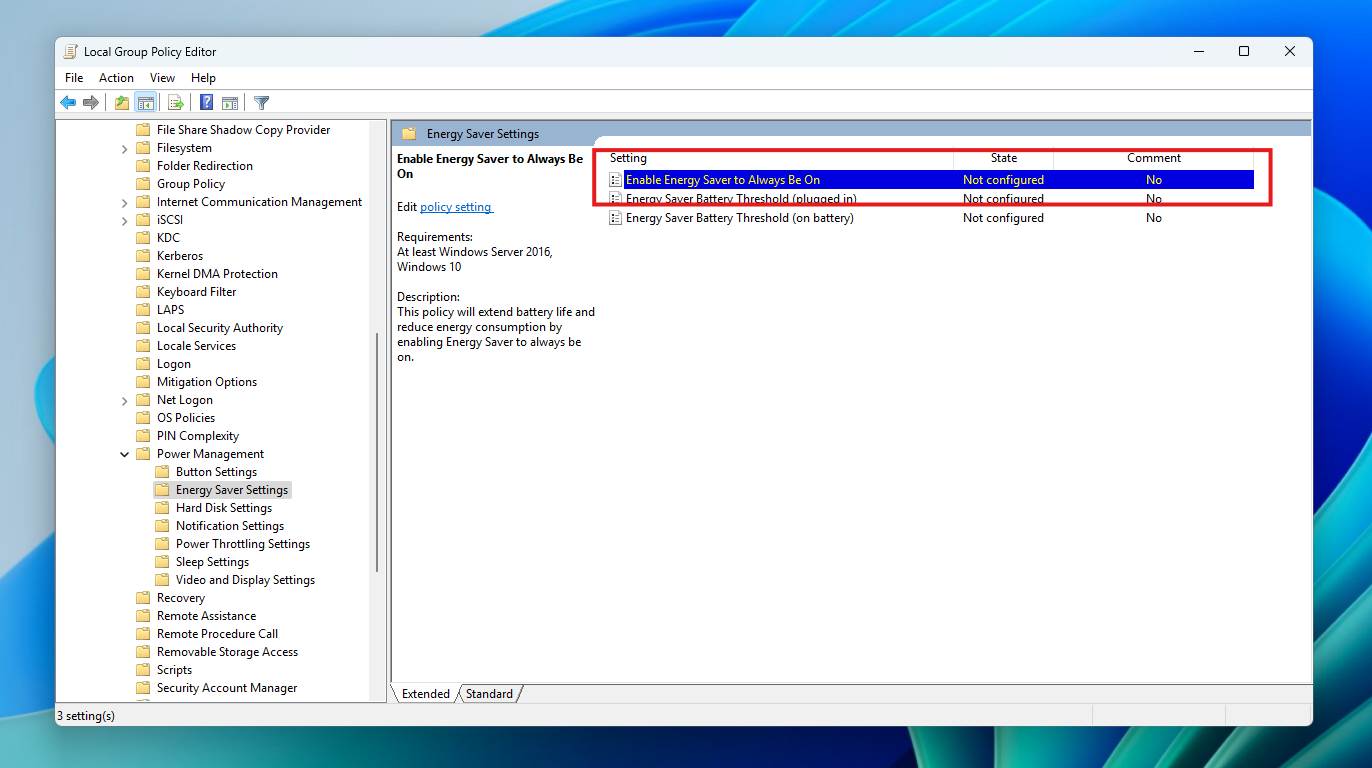
Hello Windows Insiders, today we are releasing Windows 11 Insider Preview Build 26200.5581 (KB5055651) to the Dev Channel. Changes in Dev Channel builds and updates are documented in two buckets: new features, improvements, and fixes that are being gradually rolled out for Insiders who have turned on the toggle to get the latest updates as […]
Hello Windows Insiders, today we are releasing Windows 11 Insider Preview Build 26120.3950 (KB5055653) to the Beta Channel for Windows Insiders on Windows 11, version 24H2. REMINDER: Build 22635.5305 was the last update released to the Beta Channel based on Windows 11, version 23H2. All Insiders in the Beta Channel will be getting upgraded to […]
A new “Bring Your Own Installer” EDR bypass technique is exploited in attacks to bypass SentinelOne’s tamper protection feature, allowing threat actors to disable endpoint detection and response (EDR) agents to install the Babuk ransomware. […]
Microsoft warns about the security risks posed by default configurations in Kubernetes deployments, particularly those using out-of-the-box Helm charts, which could publicly expose sensitive data. […]
TeleMessage, an Israeli company that sells an unofficial Signal message archiving tool used by some U.S. government officials, has suspended all services after reportedly being hacked. […]
The Darcula phishing-as-a-service (PhaaS) platform stole 884,000 credit cards from 13 million clicks on malicious links sent via text messages to targets worldwide. […]