Whether you’re a new student, a thriving startup, or the largest enterprise, you have financial constraints, and you need to know what you’re spending, where it’s being spent, and how to plan for the future. Nobody wants a surprise when it comes to the bill, and this is where Microsoft Cost Management comes in. We’re always looking […]
Category Archives: News
Microsoft’s AI agents are at the forefront of a significant transformation in modern business operations. These intelligent agents automate routine tasks, helping employees by freeing up valuable time to be more efficient, productive, and empowered to drive business—and industries are discovering their value. Across sectors such as finance, healthcare, and manufacturing, AI agents handle tasks […]
Hackers are launching attacks against Palo Alto Networks PAN-OS firewalls by exploiting a recently fixed vulnerability (CVE-2025-0108) that allows bypassing authentication. […]
Cybersecurity researchers have disclosed a new type of name confusion attack called whoAMI that allows anyone who publishes an Amazon Machine Image (AMI) with a specific name to gain code execution within the Amazon Web Services (AWS) account. “If executed at scale, this attack could be used to gain access to thousands of accounts,” Datadog […]
The North Korean threat actor known as the Lazarus Group has been linked to a previously undocumented JavaScript implant named Marstech1 as part of limited targeted attacks against developers. The active operation has been dubbed Marstech Mayhem by SecurityScorecard, with the malware delivered by means of an open-source repository hosted on GitHub that’s associated with […]
Attackers are now targeting an authentication bypass vulnerability affecting SonicWall firewalls shortly after the release of proof-of-concept (PoC) exploit code. […]
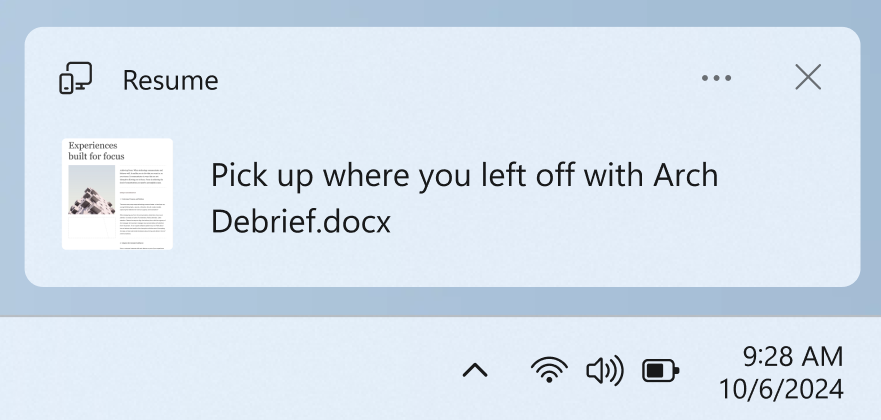
Hello Windows Insiders, today we are releasing Windows 11 Insider Preview Build 22635.4945 (KB5052084) to the Beta Channel. Please note this build will only be provided to Windows Insiders in the Beta Channel who did not upgrade to receiving updates based on Windows 11, version 24H2. Changes in Beta Channel builds and updates are documented in […]
Hello Windows Insiders, today we are releasing Windows 11 Insider Preview Build 26120.3281 (KB5052086) to the Dev and Beta Channels. As a reminder – we’re also offering this same the same Dev Channel updates based on Windows 11, version 24H2 to Windows Insiders in the Beta Channel. These updates will be optional at first, so […]
A free-to-play game named PirateFi in the Steam store has been distributing the Vidar infostealing malware to unsuspecting users. […]
CSA’s Cloud Controls Matrix (CCM) is a cybersecurity control framework for cloud computing. It contains 197 control objectives structured into 17 domains that cover all key aspects of cloud technology. You can use CCM to systematically assess a cloud implementation. CCM also provides guidance on which actors within the cloud supply chain should implement which […]