Microsoft today released security updates to fix at least 117 security holes in Windows computers and other software, including two vulnerabilities that are already seeing active attacks. Also, Adobe plugged 52 security holes across a range of products, and Apple has addressed a bug in its new macOS 15 “Sequoia” update that broke many cybersecurity […]
Category Archives: Latest Warnings
Auto Added by WPeMatico
The FBI is warning timeshare owners to be wary of a prevalent telemarketing scam involving a violent Mexican drug cartel that tries to trick people into believing someone wants to buy their property. This is the story of a couple who recently lost more than $50,000 to an ongoing timeshare scam that spans at least […]
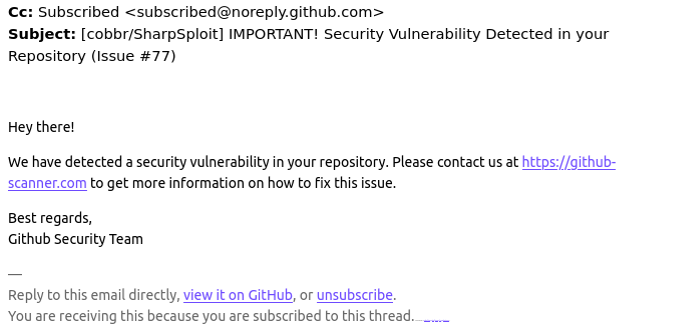
Many GitHub users this week received a novel phishing email warning of critical security holes in their code. Those who clicked the link for details were asked to distinguish themselves from bots by pressing a combination of keyboard keys that causes Microsoft Windows to download password-stealing malware. While it’s unlikely that many programmers fell for […]
Scammers are flooding Facebook with groups that purport to offer video streaming of funeral services for the recently deceased. Friends and family who follow the links for the streaming services are then asked to cough up their credit card information. Recently, these scammers have branched out into offering fake streaming services for nearly any kind […]
An old but persistent email scam known as “sextortion” has a new personalized touch: The missives, which claim that malware has captured webcam footage of recipients pleasuring themselves, now include a photo of the target’s home in a bid to make threats about publishing the videos more frightening and convincing. This week, several readers reported receiving […]
A Little Sunshine, Black Lotus Labs, Bronze Silhouette, Christopher Wray, CVE-2024-39717, Cybersecurity & Infrastructure Security Agency, Federal Bureau of Investigation, Insidious Taurus, Internet of Things (IoT), Krebs, KV-botnet, Latest Warnings, Lumen Technologies, Michael Horka, national security agency, News, Ryan English, Security, The Coming Storm, U.S. Department of Justice, Versa Director 22.1.4, Volt Typhoon
New 0-Day Attacks Linked to China’s ‘Volt Typhoon’
Malicious hackers are exploiting a zero-day vulnerability in Versa Director, a software product used by many Internet and IT service providers. Researchers believe the activity is linked to Volt Typhoon, a Chinese cyber espionage group focused on infiltrating critical U.S. networks and laying the groundwork for the ability to disrupt communications between the United States […]
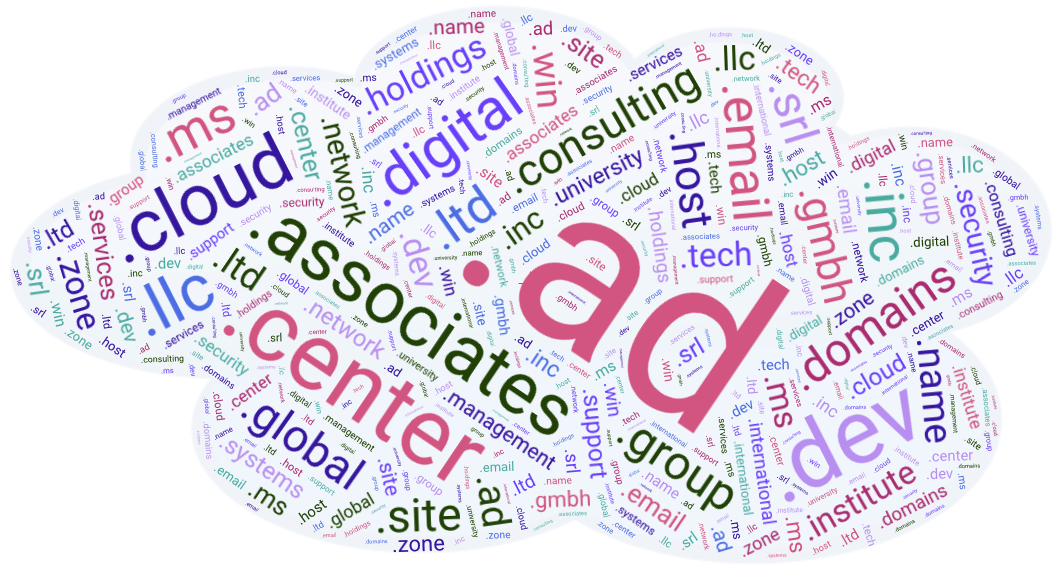
A Little Sunshine, Active Directory, Andorra, DNS name devolution, Krebs, Latest Warnings, Memphis Real-Time Crime Center, memrtcc.ad, Mike Barlow, Mike O'Connor, namespace collision, News, Philippe Caturegli, Security, Seralys, The Coming Storm, Web Fraud 2.0, Web Proxy Auto-Discovery Protocol, wpad.ad, wpad.dk
Local Networks Go Global When Domain Names Collide
The proliferation of new top-level domains (TLDs) has exacerbated a well-known security weakness: Many organizations set up their internal Microsoft authentication systems years ago using domain names in TLDs that didn’t exist at the time. Meaning, they are continuously sending their Windows usernames and passwords to domain names they do not control and which are […]
More than a million domain names — including many registered by Fortune 100 firms and brand protection companies — are vulnerable to takeover by cybercriminals thanks to authentication weaknesses at a number of large web hosting providers and domain registrars, new research finds. Image: Shutterstock. Your Web browser knows how to find a site like […]
Google says it recently fixed an authentication weakness that allowed crooks to circumvent the email verification required to create a Google Workspace account, and leverage that to impersonate a domain holder at third-party services that allow logins through Google’s “Sign in with Google” feature. Last week, KrebsOnSecurity heard from a reader who said they received a […]
.top, A Little Sunshine, Anti-Phishing Working Group, Dave Piscitello, Interisle Consulting Group, Internet Corporation for Assigned Names and Numbers, Jiangsu Bangning Science & Technology Co. Ltd, Krebs, Latest Warnings, News, Security, The Coming Storm
Phish-Friendly Domain Registry “.top” Put on Notice
The Chinese company in charge of handing out domain names ending in “.top” has been given until mid-August 2024 to show that it has put in place systems for managing phishing reports and suspending abusive domains, or else forfeit its license to sell domains. The warning comes amid the release of new findings that .top […]