As cloud adoption continues to reshape the IT landscape, ensuring cloud environments are secure and compliant is critical. However, a cybersecurity audit specific to cloud computing introduces unique challenges, given the complexities of shared security responsibilities between cloud providers and customers. Fortunately, CSA offers training and certificate programs designed to enhance auditors’ abilities to assess […]
Monthly Archives: October 2024
The latest generations of Intel processors, including Xeon chips, and AMD’s older Zen 1, Zen 1+, and Zen 2 microarchitectures on Linux are vulnerable to new speculative execution attacks that bypass existing ‘Spectre’ mitigations. […]
In 2024, the Federal Communications Commission (FCC) launched the K-12 Cybersecurity Pilot Program, a groundbreaking initiative backed by $200 million in funding. Learn more from Cynet about how schools and libraries can apply to this program. […]
North Korean information technology (IT) workers who obtain employment under false identities in Western companies are not only stealing intellectual property, but are also stepping up by demanding ransoms in order to not leak it, marking a new twist to their financially motivated attacks. “In some instances, fraudulent workers demanded ransom payments from their former […]
Originally published by Pentera.Cryptomining has surged in popularity, driven by the growing value of cryptocurrencies like Bitcoin and Ethereum. With leaked credentials easier than ever to acquire, attackers are looking for ways to profit, which has led to a rise in malicious cryptomining, or cryptojacking. This is where attackers hijack computer resources to mine cryptocurrency […]
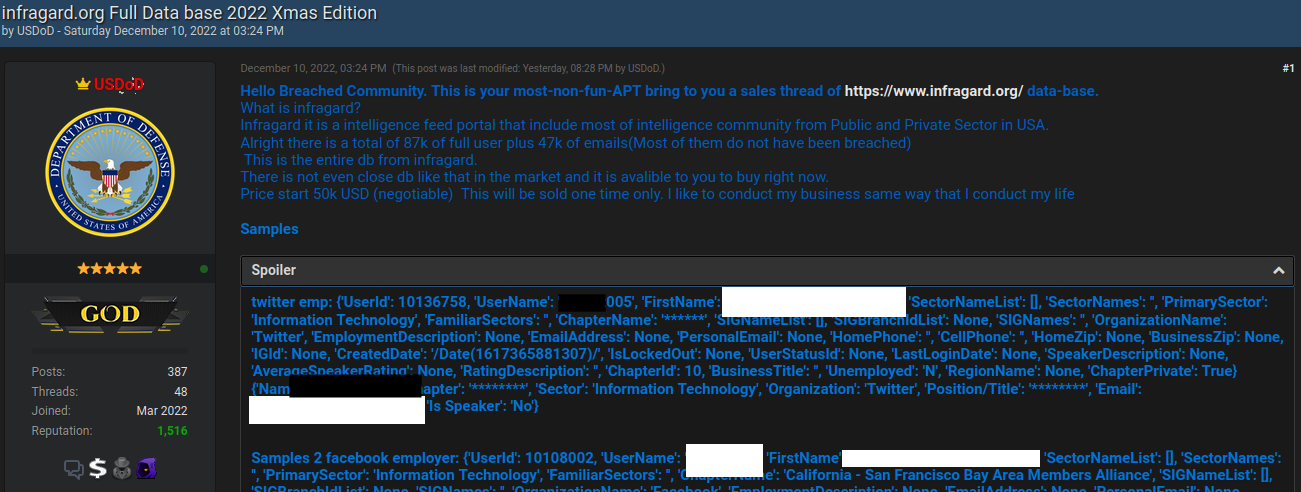
Brazilian authorities reportedly have arrested a 33-year-old man on suspicion of being “USDoD,” a prolific cybercriminal who rose to infamy in 2022 after infiltrating the FBI’s InfraGard program and leaking contact information for 80,000 members. More recently, USDoD was behind a breach at the consumer data broker National Public Data that led to the leak […]
Picture your company’s data as a vast, complex jigsaw puzzle—scattered across clouds, devices, and networks. Some pieces are hidden, some misplaced, and others might even be missing entirely. Keeping your data secure in today’s fast-evolving landscape can feel like an impossible challenge. But there’s a game-changing solution: Data Security Posture Management (DSPM). Think of it […]
Written by Abel E. Molina, Softchoice.”An ounce of prevention is worth a pound of cure.” – Benjamin FranklinIn the digital age, our lives are intricately tied to the online world, from managing finances to sharing moments with loved ones. Yet, with the convenience of the internet comes a significant risk: cyber threats. As the famous […]
Cybersecurity and intelligence agencies from Australia, Canada, and the U.S. have warned about a year-long campaign undertaken by Iranian cyber actors to infiltrate critical infrastructure organizations via brute-force attacks. “Since October 2023, Iranian actors have used brute force and password spraying to compromise user accounts and obtain access to organizations in the healthcare and
Threat actors are leveraging fake Google Meet web pages as part of an ongoing malware campaign dubbed ClickFix to deliver infostealers targeting Windows and macOS systems. “This tactic involves displaying fake error messages in web browsers to deceive users into copying and executing a given malicious PowerShell code, finally infecting their systems,” French cybersecurity company […]